
Use of cloud services is growing fast and evolving even faster. To adapt…
-
Pay attention to cloud performance and management
Before you shift anything (else) to a cloud… Examine your risks and generate strategic policies accordingly. Example: if cloud services approvals take too long, you might inadvertently be encouraging dangerous shadow IT. Use cloud monitoring to track and manage cloud services, applications, and infrastructure . Often available from your cloud provider, these tools deliver data on cloud performance, security, resource consumption, end-user experience, and customer behavior. Look out for under-utilized cloud capabilities. Cloud providers able to customize your service level agreement (SLA) can help keep your cloud performance humming and your bill under control. Consider co-location in edge computing. Co-lo systems in managed data centers provide easy connectivity to high-speed Internet services as well as public cloud and SaaS options. Beware cloud vendor lock-in. Some vendors create services captive to their environments.
-
Adapt your data management practices to the clouds
To manage data across all platforms, regardless of where it originates… Adjust your data governance policies and data standards to apply to all datasets wherever they may be. Prioritize cloud data integration requirements so your data integration toolset supports popular cloud-based application and platform protocols, interfaces, and multiple metadata types as well as metadata-poor sensor and IoT data. Plan and implement your cloud-optimized data management infrastructure before migrating to the clouds. Data integration tools and architectures need to address data quality, metadata, master data, and varying data speeds.
-
Take cloud security seriously
Cloud providers are responsible for some – but not all – cloud security. Here, for instance, is how public cloud vendor Microsoft sees it:
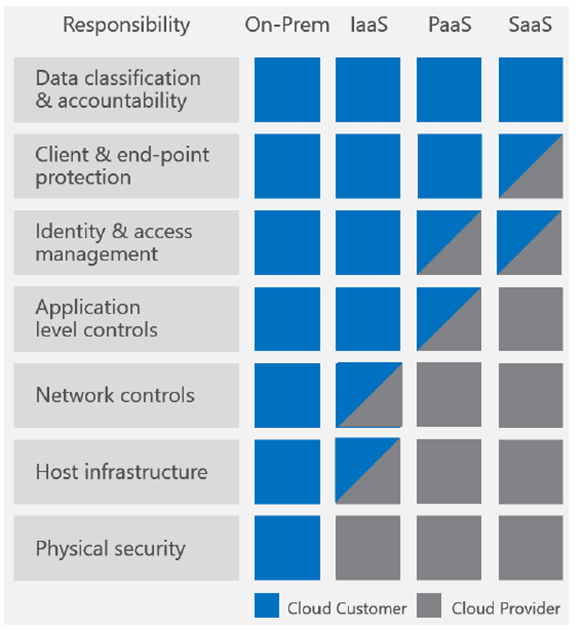
To keep up your end …
Understand your providers’ cloud security measures and ensure they carry the certifications you require for regulatory compliance.
Enforce cloud security policies – preferably via automated solutions – that delineate who can use cloud services and what data may be cloud-stored.
Deploy cloud-capable identity/access management capabilities that define and enforce policies, including role-based permissioning and multi-factor authentication.
Secure endpoints and use cloud-capable intrusion detection/prevention .
Encrypt your data, both when at rest and when in motion.
Continuously train all staff to spot social engineering attempts, and teach them the dangers of shadow IT.
Conduct regular audits and penetration testing.
-
Find a trusted cloud technology partner
Unless you have highly trained IT staff with cloud technology expertise, don’t go it alone. Instead, vet cloud technology consultants to find one you can trust that’s committed to both technology and business breadth and depth. You’ll save plenty of money and hassle if you do.
