
Targeted zero-day attacks are proliferating — and focusing more and more on smaller businesses because these tend to have weaker defenses. Some security experts say that if your security posture can be bypassed with custom malware, you’re probably already compromised.
Zero-day attacks get their edge from speed, since reactive countermeasures that depend on threat signatures — such as patching and tools like antivirus software and intrusion prevention — can’t be updated fast enough to keep up with an attack in its early stages. The best-known zero-day attack so far is Stuxnet, renowned for its use of not one but an unprecedented four zero-day vulnerabilities (one of these enables it to spread via USB drives, then there’s a print spooler remote code execution vulnerability plus two local privilege escalation vulnerabilities).
The majority of today’s malware encounters occur via the Web, and many zero-day attacks take advantage of threat development Web sites, toolkits, and frameworks to quickly tweak known threats into new, unknown threats — called blended threats — able to thwart signature-based countermeasures.
When these are delivered via botnets that run covertly on networks and systems, sensitive data can often be gathered for long periods without detection. And increasingly, kernel-level exploits called rootkits are also being used because they mask the presence of other types of malware.
What can you do about zero-day attacks?
Layer your defenses, so what one defense doesn’t uncover another will. This means access control lists, firewalls, data loss prevention capability, port knocking, intrusion prevention systems, whitelisting, religiously updating and patching OSs and all software, training users in security-aware behaviors, and encrypted communication.
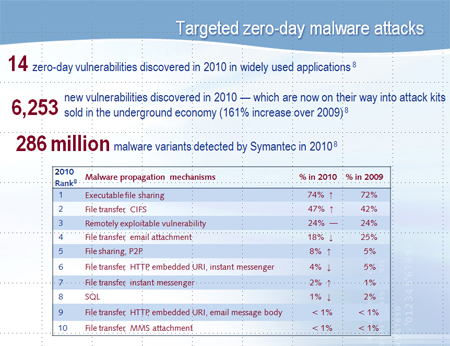
Infographic source: Symantec Internet Security Threat Report, April 2011, Symantec
