
In this age of the restless customer – not merely digital-centric but also “adventurous, experimental, and downright fickle” – I notice three crucial cloud-shaping trends:
1 The shadow IT underground
Business units everywhere buy cloud services without IT department approval in a mass decentralization of IT “authority.”
Why? Because these cloud services help business units stay competitive, responsive, and innovative at a time when 40% of consumers have expressed “a high willingness and ability to shift spend,” and another 25% are leaning that way .
Customer fuses are shorter than ever, too. Those “who experience disgust, anger, or a feeling of neglect during a brand interaction are about eight times more likely not to forgive that company.”
The fallout from so much shadow IT is immense:
Bring your own device ( BYOD ) has blossomed into bring your own apps (BYOA), – and even D(develop)YOA . Says one Gartner analyst: “Over 90% of knowledge workers who own a personal smartphone or tablet use third-party apps for work-related tasks.”
Risky, to be sure. But attempting to quash shadow IT will only drive it further underground – where it’ll continue to spawn with plenty of help from…
2 IoT
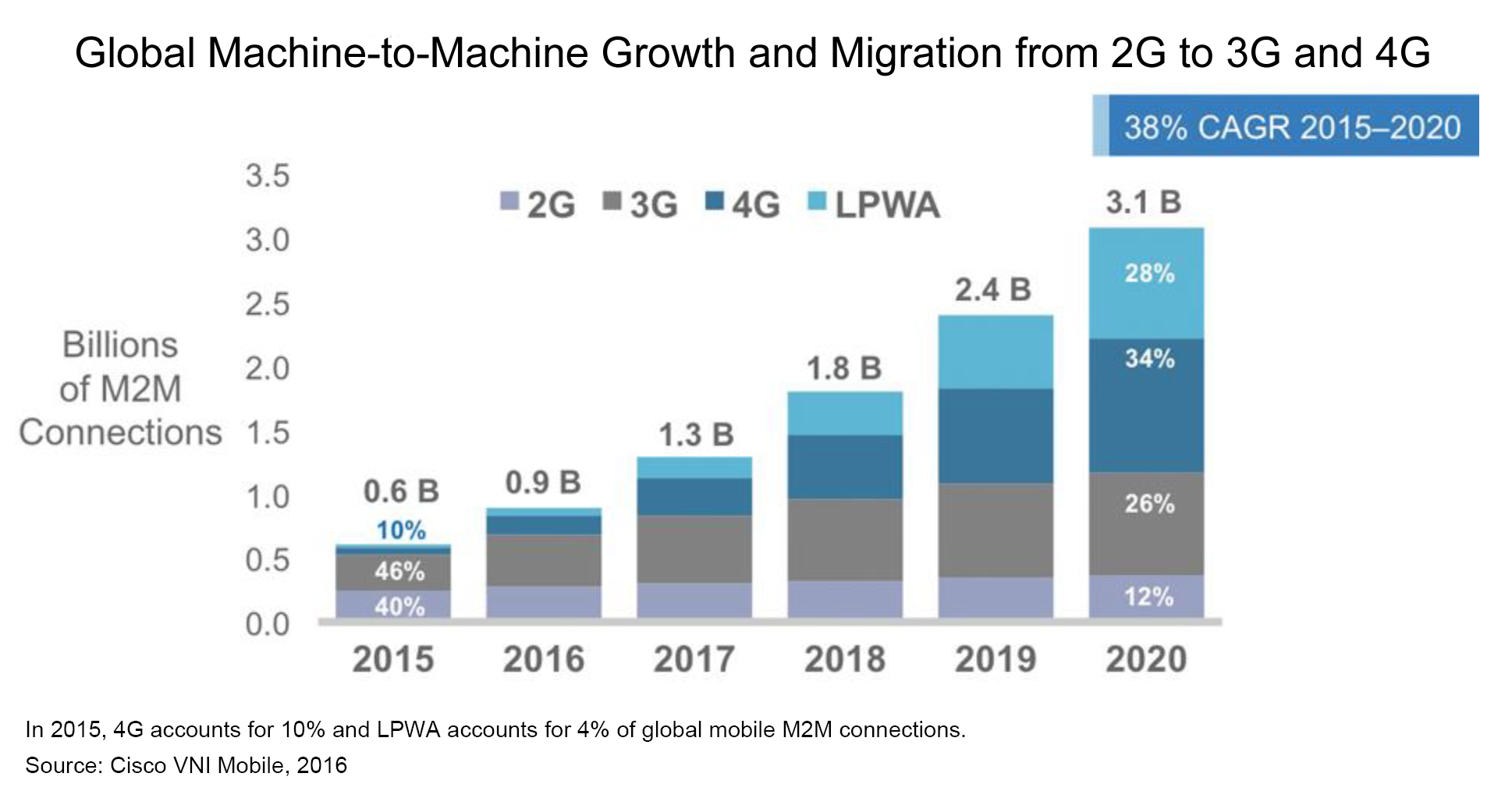
All the major public clouds have Internet of Things (IoT)platforms now, and for good reason: by 2020, there will be more than 600 million wearable devices and 3.1 billion M2M (machine-to-machine) connections.
IoT applications are already exploiting this burgeoning connectivity, gathering and analyzing vast amounts of cloud data for opportunities. The possibilities are powerful, even irresistible. But they present serious challenges, too:
- > Complexity that can overwhelm you if you wait too long to address it, since IoT solutions are built on microservices and distributed across edge devices, gateways, and cloud services with divergent standards, protocols, and software.
- > Exposure to security threats – both data breaches and hijacked IoT devices used as weapons of DDoS.
3 Desperately seeking cloud security
Within two years, the cost of data breaches globally will top $2 trillion . No question that cloud environments and the endpoints linked to them are profoundly tempting targets for cybercriminals.
So holistic, next-gen cloud security is critical. That means end-to-end, designed for mobility, encompassing every single digital and data point, using virtual security services built on contextual, predictive intrusion prevention and detection services (IPS/IDS) and intelligent data loss prevention (DLP) .
It also means cloud security that’s baked into innovative infrastructures that exploit the leading-edge technologies – such as software-defined networks (SDNs), containerization, microservices, network function virtualization (NFV), hyperconverged infrastructures (HCIs), and so on – that power key cloud integration, cost-efficiency, and collaboration capabilities.
Competent cloud services providers , of course, are hard at work right now making this happen – and are succeeding significantly enough that their cloud environments are perceived by many as more secure than most organizations’ in-house data centers.
In upcoming posts, I’ll focus on what these transforming cloud trends mean for your organization’s digital-centric future .

