
Malware comes in many flavors. I’m focusing now on one of the most pernicious, advanced persistent threats (APTs), because these frequently use the techniques of zero-day attacks to remotely manipulate a system while remaining virtually invisible to standard defenses.
This raises major new malware detection challenges. Says one security expert : “If you have something of interest and you’re not seeing APT attacks … it is probably not that they are not occurring or that you’re safe. It’s more likely that you may need to rethink your detection capabilities.”
What’s important to understand about advanced persistent threats is that part about their virtual invisibility. Because they’re so hard to spot, an organization can be plagued by a single APT exploit for months, even for years — and even after becoming aware of the attack. We describe these attacks as persistent because instead of going away, they react to your incident response by evolving and seeking out new vulnerabilities and weaknesses.
These sorts of threats come from adversaries with plenty of resources who do methodical centralized planning to take advantage of the specific systems, applications, configurations, and even the people in a specific organization. Often, their execution is decentralized. We call these threats advanced because they’re so resilient, adaptive, and patient.
To defend against them, you’ll need to add to your layered defenses by deploying computer security incident response capabilities that
- Produce, collect, and query as many logs as possible from a security perspective,
- Conduct deep packet inspection of all the important choke points on your network,
- Quickly query network connections across all network choke points,
- Can analyze malware, and
- Enable trusted relationships with other organizations to share intelligence on events (e.g., the Forum of Incident Response Teams, first.org).
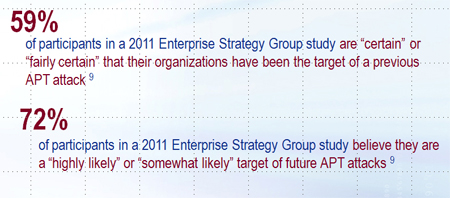
Infographic source: Enterprise Strategy Group press release, November 1, 2011

